Hacker exposes ‘phone-tracking’ service data for thousands of law enforcement agencies
A breach of Securus Technologies, a prison technology company that has been known to work with law enforcement agencies to provide phone-tracking services, has shed light on vulnerabilities affecting potentially thousands of county and city law enforcement agencies across the country.
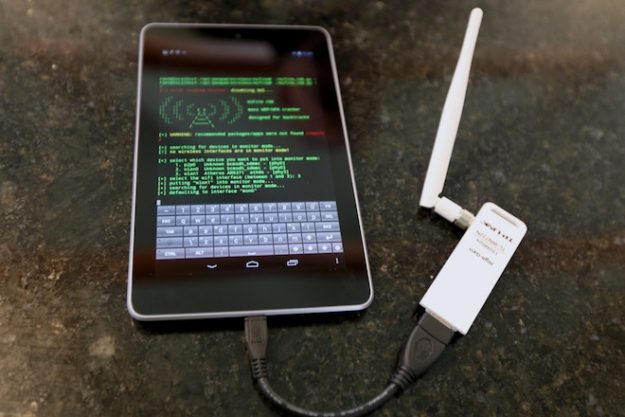
Motherboard reported earlier this month that a greyhat hacker gained access to an internal Securus spreadsheet that contained at least 2,800 pieces of confidential user data dating back to 2011, including usernames, email addresses, phone numbers, hashed passwords and security questions. The hacker provided the data to Motherboard and explained the methodology used to access the company’s internal records — a fairly simple hack, Motherboard determined.
The fact that a hacker was easily able to access this data is concerning to government officials for a few reasons. One of Securus’s main services is a location-based phone tracking service; if log-in information fell into the hands of bad actors, they would gain the ability to track millions of cellular devices at the push of a button. As it happens, police have been abusing the service already — a New York Times report published earlier this month detailed the case of a former Missouri county sheriff using the service to track colleagues and judicial officials without their knowledge.
Much of the log-in data provided to Motherboard belonged to the local county and city law enforcement agencies that serve as a large clientele of Securus’s phone-tracking service, one of its multiple prison-telephone technologies.
The service is made possible by the company purchasing data from major telecom providers, like AT&T, Verizon, Sprint and others, and then re-selling it to law enforcement agencies that would not be able to legally access it otherwise. If compromised, the service would theoretically allow bad actors to see location data from millions of phones, a vulnerability that has recently raised questions from U.S. senators.
Oregon Sen. Ron Wyden asked earlier this month that the FCC “promptly investigate Securus, the wireless carriers’ failure to maintain exclusive control over law enforcement access to their customers’ location data, and also conduct a broad investigation into what demonstration of customer consent, if any, each wireless carrier requires from other companies before the carries provide them with customer location information and other data.”
According to the Motherboard story published on May 16, Securus marketed its location-based services on its website as a product that allowed law enforcement officials to monitor where inmates were calling from. The webpage for that product is no longer up , and Securus said it disabled location data access out of caution, though the company also says it has no reason to believe the data stolen by the hacker is related to the users of the location-based services product.
Motherboard reported that it could not verify whether the user data it was given was related to the location-based services product, either. Nonetheless, personally identifiable information from law enforcement agencies in Indianapolis, Minneapolis, Phoenix, and other cities were included in the data, ostensibly just a few of the approximately 3,400 total agencies, sheriff departments and correctional facilities Securus serves.
Officials from two of the 18 Minneapolis-based agencies Securus contracts told StateScoop that agency data had not been compromised. Minneapolis Police Department spokesperson Scott Seroka confirmed his agency was not compromised in the hack.
And Jon Collins, a spokesperson from the Hennepin County Sheriff’s Office, said that the jail inmate phone platform his agency uses, which is provided by Securus, was also not compromised. Collins said that the compromised platform is completely separate from his agency’s Secure Call Platform application — ruling out at least one platform that isn’t the location-based services platform.
“We have been notified by Securus that they have implemented a new security procedure that will require all users, no matter the platform, to change their passwords and confirm their ID,” Collins said.
Securus did not respond to a request for comment.