Time will tell if states’ ransomware payment bans curb threat

A law enacted in Florida earlier this month made that state the second to ban public-sector entities from paying ransomware demands.
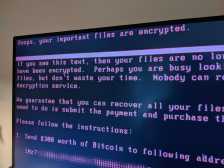
The new law, passed by legislators who’d seen multiple Florida cities pay six-figure bounties to recover encrypted data, says that any statewide agency, county government or municipality hit with extortion malware “may not pay or otherwise comply with a ransom demand.” With the law’s adoption, Florida followed North Carolina, which passed a similar law in April, in prohibiting public-sector organizations from engaging in financial transactions with ransomware actors.
Lawmakers in at least four other states — Arizona, New York, Pennsylvania and Texas — are considering bans of their own.
But even as states make these moves in another attempt to curb a nagging threat to government operations and data security, cybersecurity practitioners and legal experts have doubts that payment bans will be effective deterrents.
“It’s such a new development, we just don’t know yet,” Elise Elam, an attorney in the cybersecurity practice at the law firm BakerHostetler, told StateScoop. “It’s just too new to get a feel for whether it’ll be a deterrent for ransomware actors to target these state agencies.”
‘I just don’t see it working’
Brett Callow, an analyst at the antivirus firm Emsisoft who’s spent the past several years tracking ransomware incidents against the public sector, said he’s doubtful the laws in Florida and North Carolina will have much of an impact.
“Localized bans limited to the public sector only?” he said. “I just don’t see it working.”
Ransomware operators, Callow said, are unlikely to drop state and local governments as victims just because of a new statute. And as most originate from non-English-speaking parts of the globe, ransomware actors may sometimes be unable to distinguish between public and private organizations.
“They may not realize something called a ‘corporation’ is not a corporation in the usual sense, but a public body,” he said.
But the public sector continues to be a prime target, a fact Callow said was emphasized in June 2019, when the Florida cities of Riviera Beach and Lake City paid about a half-million dollars each to recover data and systems that had been encrypted by affiliates of the Ryuk outfit.
“I think those two payments made the attackers realize the public sector was a potentially lucrative target,” Callow said.
Some states are attempting to protect their communities, but those efforts could trip up arrangements with cybersecurity insurers — or backfire altogether by making entities not covered by the bans even more vulnerable. For insurers, the cost of a ransom is often cheaper than covering the rebuilding of an encrypted network and replacing infected technology. Meanwhile, cyber insurance premiums have been going up for years, fueled by a nonstop increase in claims by ransomware victims.
“There will be a need to restructure that relationship,” said Benjamin Wanger, a BakerHostetler counsel who co-authored a recent blog post with Elam on the Florida law. “If government entities can’t pay ransom, the risks could be greater to [insurers] in the long term. The hope is government agencies become les of a target.”
But Callow said ransomware actors could respond by ratcheting up their pressure on entities that aren’t covered by payment bans.
“Potentially it could result in an uptick in attacks on entities that can pay,” he said.
All bans not equal
Payment bans have been a divisive concept in the cybersecurity community. The White House-backed Ransomware Task Force, which published an extensive report last year on the global threat, said payments “should be discouraged as far as possible,” but could not come to an agreement on whether outright prohibitions are the ideal policy.
And the legislation behind the bans varies from state to state: North Carolina’s ban, which was implemented as part of a recent state budget, covers the entirety of the public sector, including the legislative and judicial branches, K-12 schools and the University of North Carolina. Florida’s does not include educational institutions, though it does impose a 12-hour window for state agencies and local governments to report attacks to IT and law enforcement officials.
Wanger said excluding schools, especially K-12 districts, from a payment ban is sensible, considering the services they provide and amount of data they hold on children and families. The Judson Independent School District in Texas last summer paid nearly $550,000 to decrypt its systems and prevent the publication of stolen student and staff data, one of many incidents of K-12 organizations buckling to hackers’ financial demands.
“Given the importance of schools, we can’t afford to have one need to rebuild all its systems,” he said.
Payment bans are not necessarily an immutable rule: A bill passed earlier this year by the Pennsylvania Senate outlaws the use of taxpayer money to pay off a demand, but would allow exceptions “in the event of a declaration of disaster emergency” by the governor’s office.
The two ransomware ban laws already passed North Carolina and Florida, and the few more under consideration in statehouses elsewhere are still brand-new, untested tools in an ongoing struggle. They could, Elam and Wanger said, could encourage more adoption of protective strategies like multi-factor authentication, endpoint detection tools and offline backups.
“Really what will show whether it’s working and have the desired effect will just be over time,” Elam said.