- Sponsored
- County & Local
4 reasons SLTTs need network monitoring systems
Ransomware attacks targeting U.S. state, local, tribal and territorial government entities (SLTTs) have been on the rise since 2018. It is essential for these organizations to have a comprehensive cyberdefense program in place.
From creating incident response plans and offering cybersecurity training, to implementing a network security monitoring service for identifying malicious activity — each piece plays an important part in a true defense-in-depth strategy to protect the information and data of citizens. Network monitoring solutions are a crucial way to protect SLTTs against attacks from cybercriminals.
Albert is a unique and cost-effective Intrusion Detection System (IDS) that is only offered to SLTTs through the Center for Internet Security (CIS). This network monitoring and management solution provides automated alerts on both traditional and advanced network threats by CIS’s Security Operations Center (SOC).
Many SLTTs throughout the country have embraced Albert, and there are four major reasons why Albert network monitoring is their preferred solution.
1. Quickly identity malicious activity
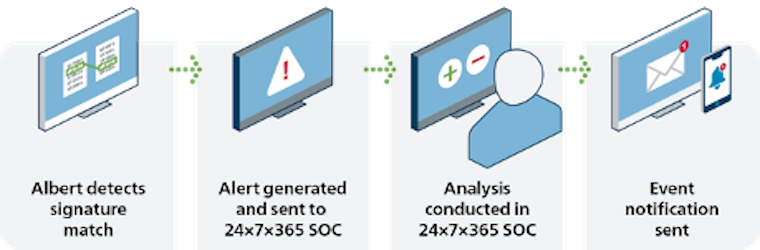
Albert uses a unique and targeted SLTT focused signature set to help ensure sensors rapidly identify and alert on potentially malicious traffic on a network. The average time it takes the SOC to receive, analyze, and notify an affected organization is less than 7 minutes.
This brief interval allows organizations to quickly investigate potential compromises, remediate and minimize impact from cyberthreats.
2. A cost-effective solution
Albert can run on commodity hardware. This, along with the expertise of the CIS SOC, provides a full-service, cost-effective solution for SLTTs.
3. Identifying trends
By monitoring a large number of SLTT networks, trends can be observed and incorporated into other CIS services and products that benefit the entire SLTT community. SLLT organizations utilize Albert’s comprehensive monthly activity report summarizing the activity identified by their sensor.
4. Monitoring, management, and support
Around-the-clock support is essential for SLTT organizations. They require a team of specialists who can manage systems and communicate with them quickly and effectively. All Albert network monitoring, as well as full management of the sensor, is handled by the CIS SOC.
When a potential threat is identified, Albert generates an alert that is sent to the SOC. A CIS analyst reviews and validates the alert for malicious activity and notifies the affected organization. By utilizing NetFlow logs, the SOC can retroactively search for newly identified malicious activity and notify the impacted entity for investigation and remediation.
Albert network monitoring and management solution, CIS
The Albert network monitoring and management solution is available to U.S. state, local, tribal and territorial (SLTT) entities, including public education institutions, critical infrastructure, and emergency response services.
Find out more about how Albert works.
This article was produced and sponsored by the Center for Internet Security.




