States need to embrace cybersecurity framework, experts say
CINCINNATI — Too few states have meaningful response plans in place to address common cybersecurity risks, a pair of public sector security experts warned at an IT industry forum Wednesday. And with few exceptions, state IT departments continue to concentrate too much of their resources on prevention and not enough on monitoring and response, they said.
Cybersecurity is no longer “just about perimeter defense,” Stephen Ellis, global public sector marketing lead for RSA, said at a National Association of State Technology Directors conference here. Increasingly, it’s making sure everyone knows, if there are “rogue actors on your network, what steps do you have in place to respond to their activity.”
According to data gathered by RSA, the enterprise security division of EMC, states have a long way to go. On average, roughly 80 percent of state IT security budgets currently go toward prevention measures, with only 15 percent going toward monitoring and 5 percent toward response, said Jacklyn Wynn, RSA’s vice president for global public sector strategy.
She said that state IT departments need to shift their approach, so that one-third of their resources goes toward monitoring and another third toward response, leaving the balance for prevention.
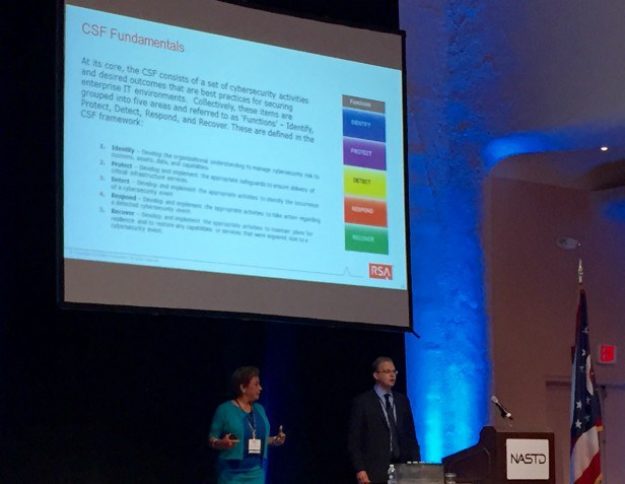
“State IT organizations also need to develop a roadmap that aligns with the NIST Cybersecurity Framework,” a set of guidelines and controls jointly developed by the National Institute of Standards and Technology and industry experts, released last year. “The CSF is becoming a de facto requirement,” she said, noting that regulators, lawyers and insurers are increasingly using the framework as a baseline for determining whether organizations have taken reasonable measures to protect their organizations, and the public, from cyberattacks
Only about 25 percent of states have taken steps to adopt some of the CSF guidelines, Wynn told StateScoop, noting that Michigan, Massachusetts and Pennsylvania are perhaps the furthest along in assessing their cyber readiness based on the cybersecurity framework.
The framework gives senior executives and directors, not just IT leaders, a way to gauge the maturity of their organization’s cybersecurity posture. It also contains industry-recommended remedies to close gaps in an organization’s ability to identify and protect against risks, detect and respond to threats, and recover when they occur.
More is at stake than just the integrity of organization’s data and IT infrastructure. Corporate boards, as well as top government agency executives face fundamental questions of who is liable, and under what circumstances, when data breaches occur.
Those questions are growing harder to answer as more organizations rely on an expanding ecosystem of providers to deliver IT services. Wynn said that the Centers for Medicare and Medicaid Services, for example, is considering whether IT contractors working on CMS system components should be required to have cybersecurity insurance.
As organizations wrestle with how to indemnify themselves in the rapidly evolving cybersecurity landscape, the NIST cybersecurity framework is increasing becoming a point of reference and one Wynn argued states should consider more seriously.
Cybersecurity experts from NIST and industry are already at work developing additional guidelines for the framework, she said. Among the areas getting attention, she said, are identity authentication, automated indicator sharing, assessments for CSF conformity, cybersecurity workforce, data analytics and ways to align with federal agency cybersecurity practices.
“This is not just an IT risk, but a business risk,” that must be addressed, she said.
Ellis said that state organizations also need to prepare for emerging technology platforms, most notably, the risks likely to evolve as cars increasingly connect with, and feed data into, state transportation and other networks.
“The borderless enterprise is the new frontier,” he said, adding “state IT leaders need to start looking now at how they will have to defend it.”