Texas and Virginia CISOs embrace ‘whole-of-state’ cybersecurity
It’s become a bit of a stock phrase for government technology officials to refer to cybersecurity as a team sport. But increasingly, states are acknowledging that it takes more than cooperation between IT agencies and other bureaucrats to build a strong cybersecurity posture, also roping local governments, academia and the private sector into the conversation, top cybersecurity officials from Texas and Virginia said Tuesday.
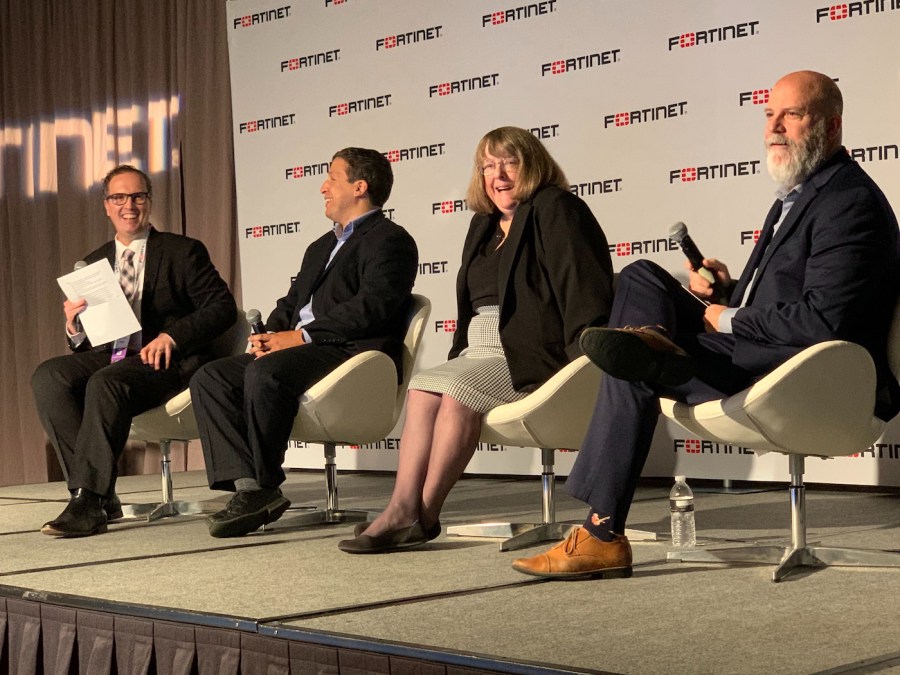
“We’ve generally understood where our threats are,” Virginia Chief Information Security Officer Michael Watson said at the Fortinet Security Transformation Summit outside Washington, D.C. “Part of the challenge is to be agile and adaptable to the business. Now we’re trying to figure out how we integrate and make cybersecurity part of our general services across the board.”
The Virginia Information Technologies Agency is responsible for providing IT services to 65 agencies, including all their cybersecurity needs, Watson said. But, he added, that doesn’t necessarily mean that the best strategies originate in government. He pointed to a number of interagency and public-private boards and councils that he and his staff sit on, not all of which are headed by a government official.
“There are councils we lead and some we sit on ex officio,” he said. “The more we are open with our peers and others, it garners good relationships.”
Watson said Virginia is among a handful of states adopting what’s known as the “whole-of-state” approach to cybersecurity, in which all stakeholders — from the state government down to small towns with minimal IT budgets — collaborate on protecting their digital assets, with the goal of pulling down the walls that often leave different entities isolated from each other in a crisis like a cyberattack or data breach.
That was the situation Texas CISO Nancy Rainosek recalled encountering when she described her initial response to a ransomware attack last August that simultaneously hit 23 local governments in her state. Although she had a clear picture of the state government’s strengths and vulnerabilities, she started with few insights into the IT security of the communities impacted by the incident.
“We’ve been measuring security at our state agencies over the last four years,” she said. “We have a great understanding of where our deficiencies are and what we’re good at. I didn’t have a handle on local government until we started having ransomware attacks and calling upon us.”
Often, that meant learning that small, resource-strapped local governments lacked even some of the most basic cybersecurity policies, like installing antivirus software on their computers. She cited a school district that suffered two ransomware attacks in a three-week span because it didn’t have antivirus protection on its servers.
Rainosek said instances like that underscore the need for better communication between different levels of government and other parties that have a stake in cybersecurity.
“This is a problem that’s bigger than all of us, so as far as leadership, there’s a lot of people really interested in doing this. All of us working together and communicating together is what it’s going to take,” she said.
Rick Driggers, the deputy assistant director for cybersecurity at the U.S. Cybersecurity and Infrastructure Security Agency, said the same culture of cooperation between different stakeholders in providing physical security to critical infrastructure hasn’t fully permeated cybersecurity.
“We all have a role to play in cybersecurity,” he said. “Sharing information broadly, especially in an anonymous way, lifts the cybersecurity posture of everyone.”
Gradually, though, state governments are getting there, Watson said.
“Most states, most CISOs that I’ve talked to, have at least some form of council or sharing group that help them connect to their local business, local stakeholders,” he said. “Sharing begets sharing.”