Unemployment fraud in Washington linked to health care ransomware
Some of the fraudulent unemployment payments that Washington state officials said they’ve paid out during the coronavirus pandemic are connected to a ransomware attack against a private health care organization, according to research published Wednesday by the private investigation firm Kroll.
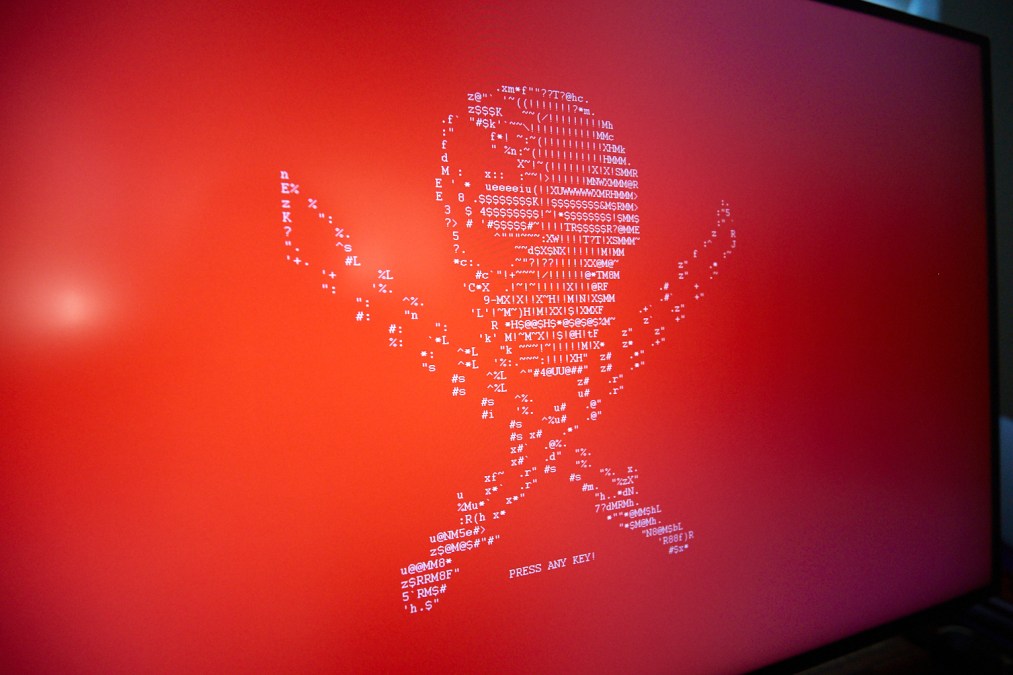
In their report, Kroll’s investigators wrote that the health care company — which they did not name — was infiltrated in early May by Russian-speaking hackers using a ransomware variant known as Mamba. The malware encrypted several machines on the health provider’s network, but unknown to the organization, it was preceded by an effort to defraud Washington’s unemployment system.
“While the victim company immediately realized it was dealing with a ransomware event, it had no idea the attackers were also using its infrastructure to file fraudulent unemployment claims with the Washington State Employment Security Department,” the report reads.
The report did not state how much was taken in this specific incident.
Washington Employment Security Department Commissioner Suzi LeVine announced May 28 that her agency had recovered about $300 million in funds that had been wrongfully paid out under the expanded benefits program implemented in response to the COVID-19 crisis. The U.S. Secret Service said last month that several states’ unemployment benefits agencies were being defrauded by phony claims filed by online scammers creating accounts with the personal identifying information of real individuals obtained on dark-web forums, but that Washington appeared to be hardest hit.
Although the Secret Service said the wave of phony unemployment payments appeared to originate in West Africa, activity from malicious actors in other countries is not uncommon, said Nicole Sette, former FBI cybersecurity analyst and senior vice president in Kroll’s cyber risk practice.
“There’s overlap between transnational organized crime groups,” she said. “There is a possibility they’re working together or just multiple groups are capitalizing on this vulnerable unemployment system.”
[ransomeware_map]
But the combination of ransomware and unemployment fraud, Sette added, appears to be a new trick.
“This is the first time we’ve seen this overlap between ransomware and unemployment fraud,” she said.
According to Kroll, once the hackers compromised the health provider on May 7, they used their access to open multiple Gmail accounts, which were then used to create profiles with Washington ESD’s benefits program. Kroll’s researchers investigating the ransomware attack were able to review browser logs that showed the hackers typed their search queries in Cyrillic, and “appeared to file claims for unemployment benefits using Personally Identifiable Information of at least two Washington state residents paired with the attacker’s Gmail accounts.”
The PII was associated with actual Washington residents, but confirmations for direct deposit payments were sent to the email accounts created by the hackers. On May 12, five days after the claims were filed, the ransomware was activated, encrypting the computer used to commit the fraud along with several others on the health care company’s network.
Mamba ransomware, which is sometimes known as HDDCryptor, exploits vulnerabilities on older versions of the Windows Server operating system. It was used in a 2016 hack of the San Francisco Municipal Transportation Agency, and in 2017 against targets in Brazil and Saudi Arabia. A newer version of the malware was identified last year by the cybersecurity firm Trend Micro.
While Kroll suspects the hackers compromised the health company using a brute-force attack against an exposed Remote Desktop Protocol port, Mamba ransomware is capable of destroying Windows event logs, allowing the actors to cover some of their tracks.
“These guys are extremely intelligent and doing their research on vulnerabilities,” said Keith Wojcieszek, a managing director in Kroll’s cyber risk practice.