Mandiant report confirms cloud server misconfiguration led to D.C. Health Link breach
An incident response report compiled by the cybersecurity firm Mandiant concluded that the data breach last month of Washington, D.C.,’s health insurance exchange was the result of a poorly configured cloud server.
The report states that the breach — detected March 6 — occurred because the Amazon Web Services server hosting a system used to file reports on D.C. Health Link’s customers had been set up so that it could be accessed by anyone who knew its IP address.
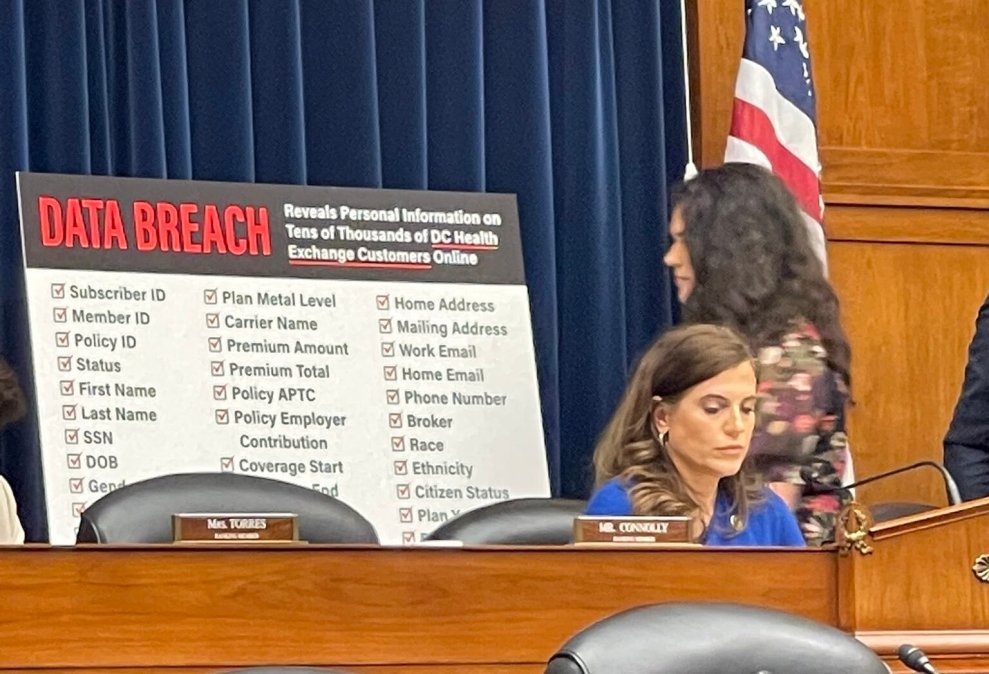
The report was the subject of a House hearing Wednesday more than a month after a user on a now-defunct hacker forum posted the sensitive data of tens of thousands of people who get their health insurance from D.C. Health Link — including numerous members of Congress, their staffers and their dependents.
“I want to say how sorry I am,” Mila Kofman, executive director of the D.C. Health Benefit Exchange Authority, the city agency that runs the Health Link marketplace, told members of two House subcommittees investigating the breach. “I know this is personal for many of you, many of your colleagues, and many staff members. We failed to prevent the theft of two reports which had sensitive personal information of our customers.”
Server misconfiguration
Kofman said Mandiant was brought in to investigate the breach on March 8 and quickly identified the source. According to the report, the server in question hosted what’s known as a Jenkins system, an open-source automation server that assists IT workers with automation tasks — in this instance, reports on D.C. Health Link’s customers, a tranche of information that included names, dates of birth, home addresses, Social Security numbers and insurance policies.
Mandiant filed its report to the D.C. Health Benefit Exchange Authority last Friday. Several members of the House Oversight and Accountability Committee and Committee on House Administration — which convened Wednesday’s hearing — said they had had seen it as well. The report, which StateScoop reviewed for this story, has not officially been made public.
According to the Mandiant report, the Jenkins system was configured with anonymous permissions, allowing unauthenticated users to download files in the workspace and read the associated logs. While those files were password-protected, Mandiant’s investigators found a reused password “in logs accessible by an unauthenticated user.”
Under questioning from House members, Kofman said the server misconfiguration was due to human error, and not any activity associated with malware, which the Mandiant report backed up. “Mandiant did not identify any artifacts associated with malware on the Jenkins system such as backdoors, or evidence of lateral movement from the Jenkins system to other systems within the DCHBX environment,” the report reads.
Breach notifications
The hacker who found the D.C. Health Link server posted 67,500 unique records from the insurance exchange on BreachForums, a site used by cybercriminals to buy and sell stolen data. That site, which was taken down last month, was accessible on the mainstream internet, despite several members of Congress referring to it Wednesday as part of the “dark web.”
Following the publication of its stolen files, D.C. Health Link sent breach notification letters to 56,415 customers — from members of Congress and their staffs on down to ordinary residents of Washington, D.C., who use it to purchase their health care policies. CyberScoop previously confirmed that more than 1,800 of the exposed records pertained to people associated with Congress, including 21 lawmakers.
Kofman also confirmed Wednesday that while D.C. Health Link customers have been offered three years of free credit monitoring, the exchange is starting to face lawsuits from some of its affected customers.
On Wednesday, House Chief Administrative Officer Catherine Szpindor, whose office is responsible for facilitating the information-sharing relationship between the lower chamber and D.C. Health Link, said the breach included 17 House members, 585 staffers and 274 dependents. She said the relationship is “compulsory in nature and is limited to the secure exchange of information required” under the 2010 Affordable Care Act, which established the system of health insurance exchanges.
‘Disturbing’ human error
The server at the heart of the breach was first set up in 2018, Kofman told Rep. Nancy Mace, R-S.C., chair of the House Oversight and Accountability Committee’s cybersecurity panel. But Kofman said she didn’t know how far back the misconfiguration allowing unfettered access went. She later said her agency has four full-time information security personnel, with additional contractors as needed.
Due to the server configurations, Mandiant was unable to find enough evidence attributing the breach to a specific actor, according to its report. However, the report reads, the BreachForums posts that shared the D.C. Health Link data named a threat actor that Mandiant said it has tracked on previous leaks and that employs a consistent set of tactics, techniques and protocols in exploiting unprotected servers.
Still, between the Mandiant report and Kofman’s testimony, several members came away from Wednesday’s hearing disappointed. House Administration Chair Bryan Steil, R-Wis., called the seven-page length of Mandiant’s report “wildly underwhelming” and said he had assumed it was only a “preliminary document.” (Kofman said the incident continues to be under investigation.)
Misconfigured cloud servers are a common headache in cybersecurity. A report Wednesday from Censys, which searches for web-connected devices, found more than 8,000 servers that had left reams of sensitive data exposed to anyone with their web addresses — just as the D.C. Health Link files appear to have been grabbed.
“It’s disturbing that human error led to the breach of 56,000 individuals’ personal data, and I don’t know what kinds of failsafes we can build into the process,” Rep. Gerry Connolly, D-Va., the top Democrat on the Oversight and Accountability cyber subcommittee, told StateScoop after the hearing.