- Sponsored
- Cybersecurity
7 steps to help prevent and limit the impact of ransomware

From local government entities to large organizations, ransomware attacks seemed to crop up everywhere in 2019. In 2020, it will take everyone’s effort to help prevent them from being successful.
Ransomware is a type of malware that blocks access to a system, device, or file until a ransom is paid. Ransomware does this by encrypting files on the endpoint, threatening to erase files or blocking system access. It can be particularly harmful when ransomware attacks affect hospitals, emergency call centers and other critical infrastructure.
Defending against ransomware requires a holistic, all-hands-on-deck approach that brings together your entire organization.
Below are seven ways organizations can help stop attacks and limit the effects of ransomware. We’ve mapped each to the applicable CIS Controls security best practices, so you can learn more on each topic.
1. Maintain backups – thoughtfully
The Multi-State Information Sharing and Analysis Center recommends backing up important data as the single most effective way of recovering from a ransomware infection. There are some things to consider, however. Your backup files should be appropriately protected and stored offline or out-of-band, so they can’t be targeted by attackers. Using cloud services could help mitigate a ransomware infection, as many retain previous versions of files allowing you to roll back to an unencrypted version. Be sure to routinely test backups for efficacy. In the case of an attack, verify that your backups aren’t infected before rolling back.
CIS Control 10 provides additional information about how to make a data recovery plan.
2. Develop plans and policies
Create an incident response plan so your IT security team knows what to do during a ransomware event. The plan should include defined roles and communications to be shared during an attack. You should also include a list of contacts such as any partners or vendors that would need to be notified. Do you have a “suspicious email” policy? If not, consider creating a company-wide policy. This will help train employees on what to do if they receive an email they’re unsure about. It can be as simple as forwarding the email to the IT security team.
View CIS Control 19 for more on incident response and management.
3. Review port settings
Many ransomware variants take advantage of Remote Desktop Protocol (RDP) port 3389 and Server Message Block (SMB) port 445. Consider whether your organization needs to leave these ports open and consider limiting connections to only trusted hosts. Be sure to review these settings for both on-premises and cloud environments, working with your cloud service provider to disable unused RDP ports.
CIS Control 9 and CIS Control 12 describe different ways your organization can control network ports, protocols, and services.
4. Harden your endpoints
Ensure your systems are configured with security in mind. Secure configuration settings can help limit your organization’s threat surface and close security gaps left over from default configurations. The CIS Benchmarks are a great, no-cost choice for organizations looking to implement industry leading, consensus-developed configurations.
Check out CIS Control 5 for more information about secure configurations.
5. Keep systems up-to-date
Make sure all of your organization’s operating systems, applications, and software are updated regularly. Applying the latest updates will help close the security gaps that attackers are looking to exploit. Where possible, turn on auto-updates so you’ll automatically have the latest security patches.
Additional information about updating and vulnerability management can be found in CIS Control 3.
6. Train the team
Security awareness training is key to stopping ransomware in its tracks. When employees can spot and avoid malicious emails, everyone plays a part in protecting the organization. Security awareness training can teach team members what to look for in an email before they click on a link or download an attachment.
More details about how to implement security awareness and training programs is available in CIS Control 17.
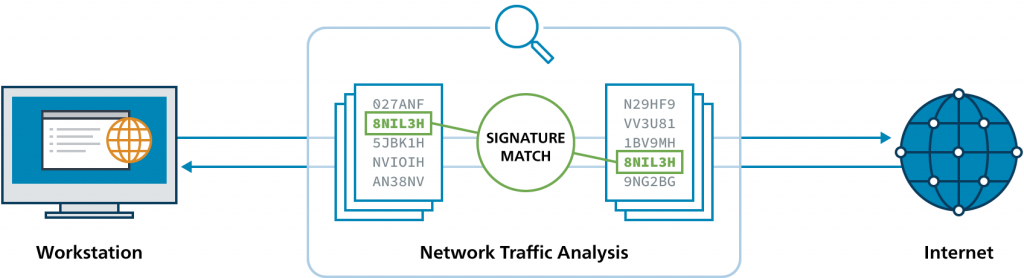
7. Implement an IDS
An Intrusion Detection System (IDS) looks for malicious activity by comparing network traffic logs to signatures that detect known malicious activity. A robust IDS will update signatures often and alert your organization quickly if it detects potential malicious activity.
CIS Control 6 and CIS Control 12 describe the maintenance, monitoring, and analysis of audit logs that’s managed by most commercial IDS.
Additionally, CIS has developed the Albert Network Monitoring technology. This is an IDS solution tailored to U.S. State, Local, Tribal, and Territorial (SLTT) government organizations. The custom signature set utilized by Albert enables it to be very effective in detecting ransomware. The signatures on Albert are updated daily to ensure organizations receive the latest threat protection.
(source: Center for Internet Security, Inc.)
When ransomware strikes, it’s important for your organization to be notified and investigate quickly. According to data from Crowdstrike, it should take mature organizations 10 minutes to investigate an intrusion. However, only 10% of organizations are able to meet this benchmark. With Albert Network Monitoring, organizations affected by ransomware are typically notified within six minutes of malicious activity.
What’s happening in those six minutes? Analysts in the CIS 24×7 Security Operations Center (SOC) are performing initial investigation by confirming malicious threat activity, reviewing any historical activity from the impacted host, gathering security recommendations for the affected organization, and notifying the affected entity with their security analysis and guidance. Cyber analysts are available to organizations using Albert around-the-clock by phone and email to answer questions, query data, and help organizations improve their defenses.
Request more information about Albert Network Monitoring.