A new interstate election security body is about to face its first major test
State election officials across the country were skittish in early 2017 when then-Homeland Security Secretary Jeh Johnson declared that, after evidence that Russian government hackers attempted to interfere with the 2016 presidential election, election systems would be deemed critical infrastructure . Johnson’s announcement meant that in future cycles, the federal government would have a role in securing voter registration databases, balloting equipment and other levers of democracy that are otherwise managed at state and local levels.
After some initial resistance from some secretaries of state, who chafed at the notion of surrendering some of their oversight to federal authorities, the designation has led to conclusions that election officials are communicating better, especially about potential cyberthreats. The National Association of Secretaries of State asked the Trump administration early on to reverse Johnson’s decision, with the organization’s then-President, Denise Merrill of Connecticut, saying it had been made “without sufficient state consultation or analysis.”
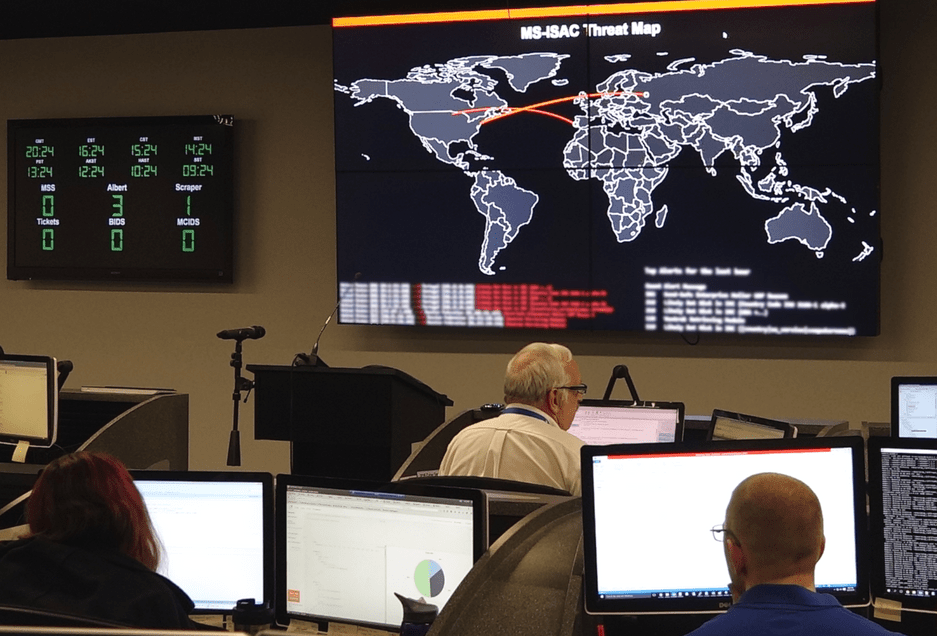
To facilitate those lines of communication, Johnson’s critical infrastructure designation eventually led to the creation in March of the Election Infrastructure Information Sharing and Analysis Center , or EI-ISAC, a DHS-backed organization run out of the nonprofit Center for Internet Security. Spun out of the Multi-State Information Sharing and Analysis Center that CIS operates at its headquarters in East Greenbush, New York, the EI-ISAC is responsible for corralling threats and vulnerabilities election officials find in their systems and offering software and hardware solutions to help members build cyberdefenses.
Overseeing the young operation is Ben Spear, who was previously a senior cyber analyst for the MS-ISAC. In an interview with StateScoop conducted two weeks before Election Day, Spear explained how he’s getting state and local governments to sign up, what members are getting out of it and how people will know if it worked or not when they wake up on Nov. 7.
It’s been about seven months since the EI-ISAC was organized. How has it gone so far?
Far better than I could’ve imagined. In just seven months we have all 50 state election boards and over 1,200 jurisdictions signed up, the enthusiasm within the election community for this has been fantastic. They’re really engaged in election security. And for me, I’ve been telling people that I’m somewhat jealous of election officials. They’re so passionate about the job they do. And security’s an important part of that because they take that responsibility of the sanctity of the vote. They’ve taken on this challenge with much vigor.
But when elections were declared critical infrastructure, there was pushback from the states. Did you have to make a hard sell at all to get states and other levels of officials to sign up for this?
We were somewhat removed from the initial designation. We’ve come in often times, as we have with the MS-ISAC, as a bit of an honest broker. Membership in the EI-ISAC is 100 percent voluntary, it’s not mandated by anyone. I think that’s something folks are comfortable with. Since we’ve started this conversation we’ve had a good partnership with secretaries of state, state election directors, clerks and all other local [officials]. Between our knowledge and expertise regarding cybersecurity and combined with the work that CIS does, these folks know what they’re talking about.
You’ve got 1,200 jurisdictions signed up. There are about 10,000 that do elections in this country. Is getting the rest of them a matter of time or having some kind of proof of concept?
Will say from the conversation we’ve had, the number [of total jurisdictions] is closer to 8,800. Certainly, the first part I would say is that part of it is outreach. We’ve visited 30 states and Puerto Rico in the last six months to promote the EI-ISAC to state election directors. We would love to have 100 percent membership. In 18 states we have greater than 50 percent of local election office membership, which I think is a strong point. The bigger piece is states where municipalities are responsible for elections, which is 4,000 to 5,000.
Then there are some states are like Wisconsin where every municipality has its own election authority and that accounts for over 1,000 right there.
A lot of those states, a big part of it is going to be how do we communicate how they provide that value to smaller jurisdictions if they don’t have the resources. But also in a lot of those states where the municipalities are responsible, a lot of those states are going to serve as a conduit with the ISAC. As much as we’d like to have 8,800, we are reaching a broad swath of jurisdictions as it stands currently. I suspect many of the states are disseminating our products further, even if they are not members.
Let’s get into the specifics of what these governments are getting back from this new organization. What are the lines of communication like?
We like to say what we’re providing is an elections-focused cyber defense suite. First and foremost, is that we are deploying these Albert monitoring systems at the same level. A number of states are exploring deploying them on the local level as well. That gives us insight into the wider threats of the election sector, and also being able to compare that to what we see in the MS-ISAC affecting the wider local and state government sectors. So we can say this is what we’re seeing in elections, this is what we’re seeing in state government. The second leg of that stool — and it’s more than a three-legged stool — is that we are providing election-specific threat intelligence. As we receive information from our membership and they’re able to report that to us, we’re developing alerts to let our membership know about items we may be seeing that they should be thinking about and providing recommendations. We have a 24/7 security operations center where people can call in any time, and a forensics team that can provide incident response as needed.
A couple weeks ago was a report that Vermont alerted DHS it had detected a Russian IP address snooping around its voter registration database. When you hear a report like that, is that something you’re sending out to other states? Do you say, “Look out for this IP range”?
I can’t speak to a specific state, but if someone was to report to us, we’re looking and examining that information. We’re making a determination whether it’s targeted or opportunistic. If it is targeted, we’ll try to correlate it with other information we have, and if we have additional data or something we have a high concern, then we can release an alert.
Reports about how active these actors are range from them being much less prevalent than in 2016 to that it’s starting to ramp up . How would you describe the threat landscape right now?
I think the threat level we see is consistent with the level of activity we’ve seen across other state and local sectors. Per that, we do not see an increased particular threat. We are receiving reporting from our members, which is great because it means they’re trusting us. But they’re consistent with threats we’re seeing across sectors.
Were there lessons from that you were able to take over from the MS-ISAC?
We still operate a unified SOC, a unified forensics team here, internally. I think the biggest lesson for us is that trust and customer service piece. As an MS-ISAC employee what I saw is other team members go out and engage membership, and when I engage with membership they speak very fondly of the MS-ISAC and what we provide. It was important to me to establish that early on with those key stakeholders. We now have significant institutional support within the election community to serve as an authoritative source.
It’s fair to say that before 2016, most election administrators probably weren’t thinking about cyberthreats from foreign intelligence agencies. How do you train people who got into a line of work where it’s about conducting the levers of democracy to think about cyberthreats from nation-states?
I don’t try to scare folks. The reality is even if it’s a nation-state, even if it’s a sophisticated actor, many of the tactics they use are similar to what we’ve seen in cybercrime and clever security threat activity for several years. The threats haven’t really changed. It’s very important for us to try to compare those to a system they use every day. The easiest one would be a DDoS attack. We would say, “Well, you all know what it’s like on election night when everyone’s trying to see your election-night reporting.” By being able to provide that kind of context about the threats, you’re able to explain to them what they can do to mitigate those threats. They are a very engaged community, they’re very interested in learning about this stuff.
So when we wake up on Nov. 7, how are we going to know this all worked?
Based on the trends we’re seeing right now will lead to hopefully nothing happening. But to me success is that even if something does happen, the right folks respond to it immediately and we’re able to communicate what we’ve done to ensure that if something did happen, we were able to mitigate that and anything that would’ve been a cause for concern. Whether or not something does happen in 2018, cybersecurity needs to remain a focus within the election community. Even if nothing happens doesn’t mean nothing won’t happen again. The risks and threats will be out there going forward.