Cyberattacks against K-12 schools continue to worsen, says analyst
In February, the Los Angeles Unified School District disclosed that “approximately 2,000 student assessment records” were posted on the dark web, including an unspecified number of driver’s license and Social Security numbers. And in March, hackers posted data stolen from the Minneapolis public school system.
These are just two of the many documented cyberattacks schools in the United States face every year. And according to Doug Levin, founder and CEO of the K-12 Security Information Exchange, or K12 SIX, a information-sharing and analysis center, the severity and frequency of attacks is on the rise.
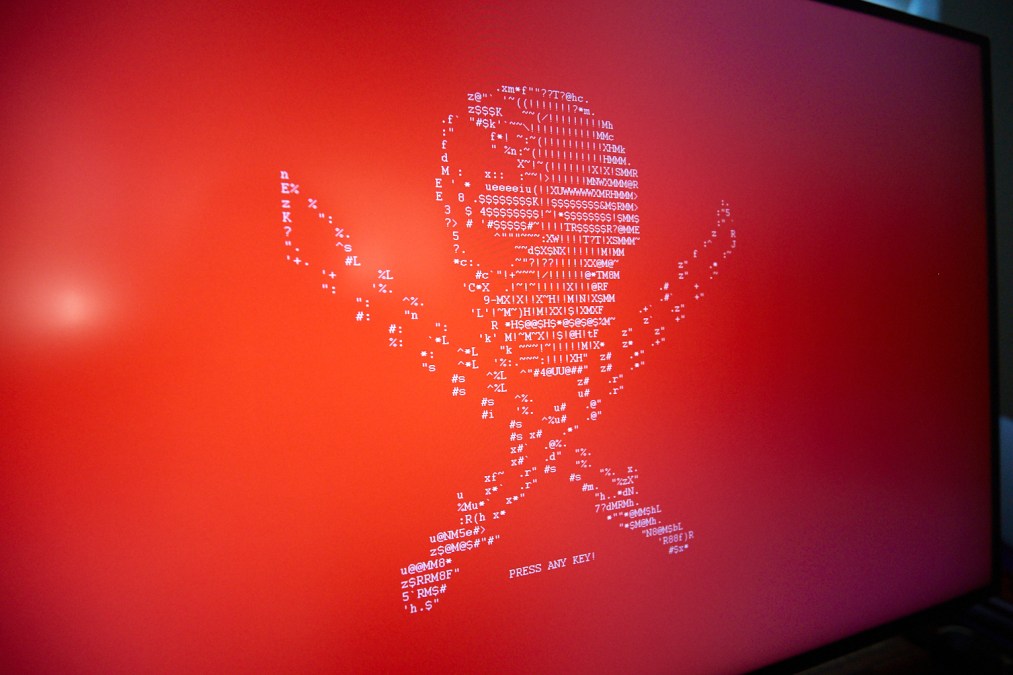
The White House and the U.S. Department of Education last month hosted the “Cybersecurity Summit for K-12 Schools” after the 2022 school year became the fourth year in a row with more than 50 ransomware attacks, including four that forced schools to cancel classes.
Doug started working in cybersecurity in 2016, when ransomware attacks were a relatively minor issue. Threat actors were only extorting $5,000-$25,000 from their victims in exchange for restoring access to victims’ systems, and the threat of posting data online hadn’t yet been popularized.
Today, that number has skyrocketed into seven figures.
“We’ve seen cyberattacks engineered to steal literally millions of dollars from school systems, through online email scams, designed to change the bank account routing information for payments,” Levin said.
‘Pinky-swear’
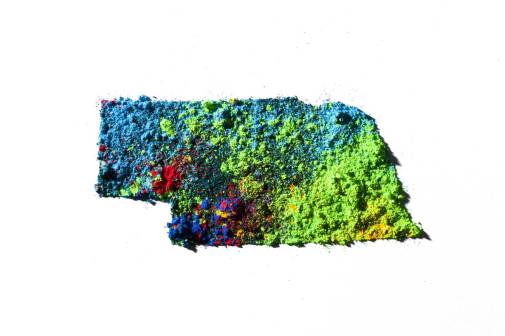
K-12 SIX tracks cyber incidents against schools using an interactive map, which from 2016-2022 documents 1,619 cyber incidents involving public schools and districts, including unauthorized breaches, ransomware attacks, phishing attacks and denial-of-service attacks, among others. Levin said he also noticed an uptick in cybercrimes against schools during the pandemic.
According to the group’s map, California, Illinois, New York and Texas — the four most-populous states in the country — are also home to school districts most vulnerable to cybersecurity threats, including the most common: ransomware. And for every ransomware incident, Levin said, data exfiltration has become commonplace — wherein actors expose sensitive data, like in the case of the cyberattacks against the Los Angeles and Minneapolis school districts.
“So not only are they being locked out of their systems, but usually some amount of data has been stolen as well. And the threat actors use that as leverage on victims to get them to pay to unlock the systems,” Levin said. “You’re also paying for the ‘pinky-swear’ that they [the hackers] won’t misuse or dump your personal information,” he added.
When a school district is compromised, it’s not just current students and staff whose information is involved, but the data of former students, staff and vendors — records that can stretch back years.
“While school districts aren’t rich organizations, they’re managing facilities, transportation, food service, buildings and have many, many employees,” Levin said. “They’re running multimillion dollar organizations – more than enough money to attract criminal interests, particularly given the relatively soft targets they represent.”
Root causes
The Biden administration acknowledged the vulnerability of school districts when in March the White House released its National Cybersecurity Strategy, outlining how training and IT upgrades can help school districts ward off cyberattacks. Rural districts are especially attractive targets for cybercriminals.
“Oftentimes they’re the largest employer in the region, but have fewer resources devoted to cybersecurity,” Levin said.
Levin said government’s slow intervention goes beyond the familiar pattern of legislation failing to keep pace with emerging technology. He said many school districts don’t understand cybersecurity, viewing it purely as a technology issue, instead of an operational one.
“When we see school districts compromised, usually the root cause is because of running unpatched or older software and IT systems that are exposed to the internet with credentials that have been compromised because school districts have not implemented a multifactor authentication,” Levin said.
Many states are taking steps to better protect their school districts, including Texas, which this month launched a portal for local governments to report cybersecurity incidents. The Alabama Department of Education recently created a list of cybersecurity requirements for local education agencies. And many other states’ IT offices are increasingly working with local governments to offer resources and support.
But, Levin said, legislators hold the power to make the biggest impact on cybersecurity for schools.
“I do think it’s important that policymakers at the federal level step up and provide schools with assistance and set some standards for schools as well, for what sorts of defenses students and families and teachers should expect and deserve from their school systems,” he said.