‘Cuba Ransomware’ attack disrupts payment provider used by state and local agencies
City and state agencies have this month begun disclosing a recent ransomware attack against a widely used payment processing service.
Bleeping Computer reported Thursday that the company known as Automatic Funds Transfer Services was hit by a ransomware attack around Feb. 3 when a group called “Cuba Ransomware” began stealing the company’s credentials and unencrypted files. According to the group’s website, it’s stolen “financial documents, correspondence with bank employees, account movements, balance sheets, and tax documents” from the company that processes paper-based payments for many state and local government agencies.
Government agencies that have reported the attack this month include the California Department of Motor Vehicles, which on Wednesday disclosed that its last 20 months of vehicle registration records may have been compromised. This includes names, addresses, license plate numbers and vehicle identification numbers, the state said, but not Social Security numbers, birthdates, voter registration information, immigration status or driver’s license information. The DMV said it stopped all “data transfers” after discovering the breach.
The Washington cities of Kirkland, Lynnwood, Monroe and Redmond, in addition to Seattle, have also put out data breach notifications in recent days connected to the attack on AFTS, along with the Seattle-area agencies of Lakewood Water District and the Port of Everett.
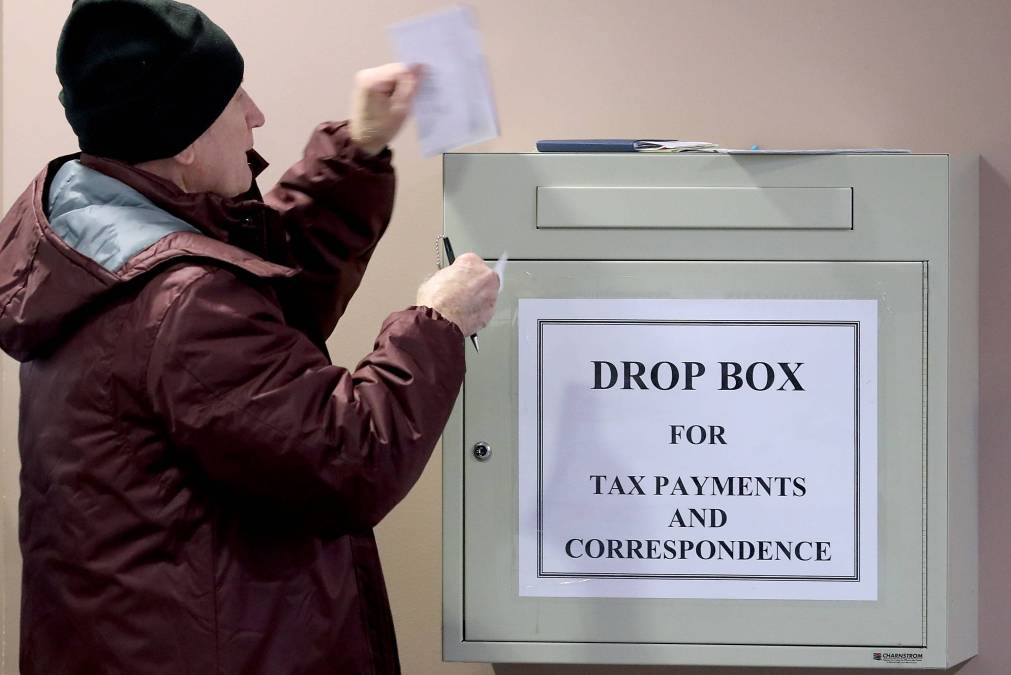
With the growing adoption of digital payment options, the recent attack’s service disruptions have been minimal. In Kirkland, for example, residents who pay their bills by mail are being instructed to instead drop off payments at the city hall or use an alternate payment method, like direct debit.
Most agencies noted in their breach disclosures that there’s no evidence that their own data was affected and that the notices were being issued out of an abundance of caution.
Yet the incident harkens back to a 2019 ransomware attack against the managed service provider TSM Consulting that resulted in simultaneous service disruptions at 22 local governments in Texas. The recently disclosed supply-chain attacks against SolarWinds, Microsoft and VMWare that granted foreign actors widespread access to the networks of federal, state and local agencies, along with private companies, further highlighted the vulnerabilities concomitant with an increasingly distributed computing environment.
The top technologists in state governments in particular have in recent years taken to referring to themselves as “brokers of services,” underscoring the increasing prevalence of digital government services that are run by third parties.
[ransomeware_map]