Before cyberattack, Baltimore saved data only on local hard drives

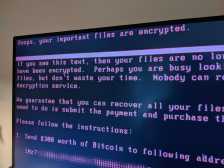
Baltimore’s IT agency could not prove that it was meeting certain performance metrics in a recent audit because the relevant data had been stored locally on employees’ computers that were corrupted by a ransomware attack that crippled the city’s municipal networks earlier this year, the city’s top watchdog said this week.
Auditor Josh Pasch told members of the Baltimore City Council on Tuesday that Baltimore City Information Technology could not turn over documentation related to four key measures, undermining BCIT’s reporting on its performance during the 2017 and 2018 fiscal years.
“Without any supporting documentation, BCIT cannot demonstrate whether the actual amounts were accurately reported … resulting in loss of confidence in data reliability presented,” the audit report says.
The measures for which data was lost include BCIT’s ability to deliver enterprise IT services to other city agencies, the number of applications removed from an aging mainframe, and the capacity of the city’s 311 hotline. The data sets were unavailable to auditors because the responsible employees saved them on their own hard drives without an external backup.
“One of the responsible personnel’s hard drive was confiscated and the other responsible personnel’s selected files were removed due to the May 2019 ransomware incident,” the audit reads. “Due to the lack of data backup, the supporting data for the four selected measures were unavailable.”
Councilmember Eric Costello, who leads the audit committee and has been critical of BCIT’s performance since the May 7 ransomware attack, was struck momentarily incredulous.
“That can’t be right. That’s real?” Costello asked Pasch.
“Are you questioning the word ‘responsible?'” Pasch replied.
“No, I’m questioning whether or not they’re storing it on their hard drive and not on a server or a cloud,” Costello responded.
Pasch’s answer did not give Costello much solace.
“One of the things I’ve learned in my short time here is that a great number of Baltimore city employees store entity information on their local computers,” said Pasch, who was appointed the city’s auditor in June.
Costello, a former federal IT auditor, was stunned that Baltimore’s IT agency would not avail itself of storage solutions meant to preserve backups in the event of a local device being rendered inoperable by a threat like ransomware.
“Wow. That’s mind-boggling to me,” he told Pasch. “Do they really understand that’s an issue? Because they’re the agency tasked with educating people that that’s the problem.”
The revelation that some of BCIT workers were not backing up files measuring the agency’s performance — and which were later lost to a cyberattack — was the latest embarrassment for Baltimore’s IT office. Earlier this month, the city’s CIO, Frank Johnson, was placed on unpaid leave. A few weeks after the ransomware attack, Johnson admitted to the City Council that BCIT did not have a disaster response plan to deal with a cyberattack the scale of the May 7 incident and said it could take nine months to draft one, an answer that Costello later told StateScoop was “completely unacceptable.”
Todd Carter, a former energy IT executive who was hired as Johnson’s deputy in early May, has been serving as interim CIO.
While Baltimore refused to pay the RobbinHood virus’ demand of 13 bitcoins — about $76,000 at the time of the attack — its recovery has been costly. City officials expect to spend about $10 million rebuilding and replacing affected systems, and take an additional $8 million hit from lost revenue.