Why the Center for Internet Security moved its storage to the cloud
In anticipation of the 2020 election, the Center for Internet Security says it plans to distribute as many as 150 additional Albert sensors, devices that monitor computer networks for intrusions, to state and local governments by the end of the year. The nonprofit has provided more than 400 such devices to agencies since it began distributing them in 2010, but as network traffic and the number of sensors has grown, the group has had to update its storage technology, a CIS employee told a conference audience on Wednesday.
CIS Chief Technology Officer Brian Calkin said the organization eventually ran out of storage space in its on-site data center at its office in East Greenbush, New York, prompting a decision in late 2017 to migrate to the Amazon Web Services cloud. Since then, he said, CIS has vastly expanded its data-collection ability and the speed at which it can research cyberthreats against states and local networks it supports.
“A query could take hours or days to even weeks to complete,” Calkin said at the AWS Public Sector Summit in Washington. “Our analysts would be looking at something on a Monday and totally forget what they were looking at by the time the results came back.”
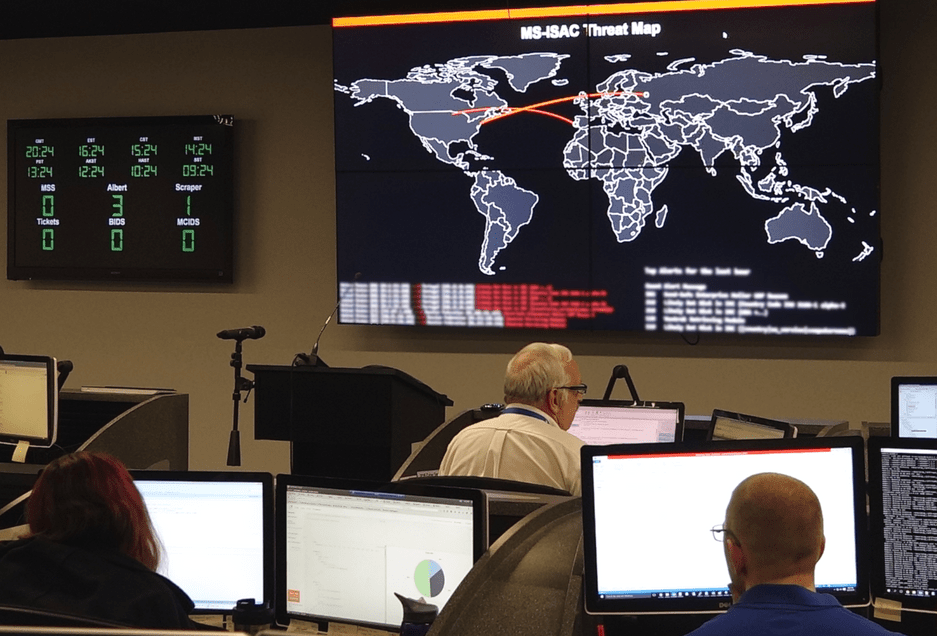
CIS builds Albert sensors from single-unit servers outfitted with open-source software that detects anomalous and malicious network activity. The data collected by the sensors is transmitted back to CIS’s secure operations center, where employees analyze the suspicious activity and issue alerts as necessary.
The reports an Albert sensor generates are similar to a phone bill. They show source and destination IP addresses and the amount of internet traffic sent, but more detailed information about the content of the internet traffic is not collected or reflected in the sensor reports.
But the amount of data generated has still proven a growing challenge for CIS, Calkin said. With more than 400 sensors distributed nationally, he said, the group is now collecting 48 million records per minute, creating an amount of data that can only be measured in petabytes — about 1 million gigabytes.
“Our [storage area network] was under-resourced in terms of speed and capability, and we didn’t just have the disk space,” Calkin said. “We were either going to build another SAN on-[premises] or go to the cloud.”
Calkin said CIS held internal doubts about shifting away from physical storage to a managed cloud service like AWS to hold the data it collects from a group of state and local governments that now numbers in the thousands.
“Because we’re the Center for Internet Security, it had to be highly secure,” he said. “It’s inherent in our name.”
But he said the experience of buying a new rack of servers, only to open the box and find they were shipped with incorrect parts, gave CIS the final nudge. The organization settled on Amazon’s S3 service, which AWS consultant Bob Strahan said can be scaled up as more data pours in and can also be outfitted with a suite of data-protection and security tools offered by Amazon and other vendors.
The biggest upshot of CIS’s move to the cloud might be the speed at which the group’s analysts can sift through the data coming from its Albert sensors. A query for all records generated by a single sensor that once took 15 minutes now takes just two minutes, Calkin said. The improvement is even starker in more complex queries: a state-government user’s request for a reading of all traffic sent to a specific IP address over a one-week period now takes just 19 minutes on AWS, compared to the 48 hours it took on the old physical servers, Calkin said.
CIS is also building a query tool that runs on a graphical interface rather than a text-based interface. In time, he said, that tool may eventually be offered through its Multi-State Information Sharing and Analysis Center and Election Infrastructure ISAC, which was formed last year as part of the response to attempts by the Russian government to hack voting systems during the 2016 presidential election. So far, the EI-ISAC has enrolled election officials in all 50 states and more than 1,600 local governments.
With that tool, he said, member governments will be able to analyze their network traffic themselves.
That might also come in handy as the number of Albert sensors in use continues to grow, especially among elections officials. The top election officials in several states, including New Jersey and Louisiana, have said they plan to install sensors at the county level before the 2020 election.




